Proof of Concept of Microsoft Edge Remote Code Execution Bug is now available
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
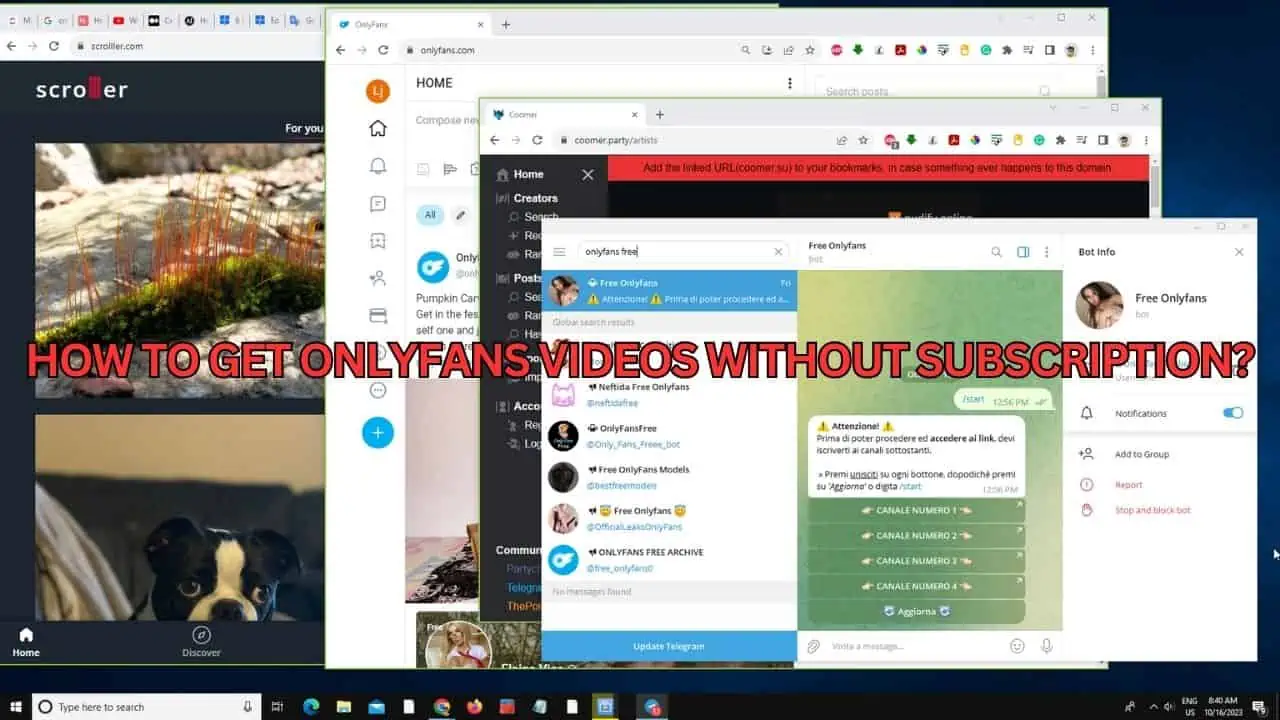
Microsoft addressed a long list of bugs on Microsoft Edge with this month’s Patch Tuesday update. Among the bugs was Microsoft Edge Remote Code Execution Bug which was discovered back in July and was reported to Microsoft via Trend Micro’s Zero Day Initiative program.
The vulnerability was discovered by security researcher Abdulrahman Al-Qabandi who started his investigations from the response to ‘mailto’ URI scheme in Microsoft Edge when he noticed that Outlook would launch with a parameter customized for the scenario at hand. Upon further investigation, he discovered a bug which allowed remote attackers to execute arbitrary code on vulnerable installations of Microsoft Edge.
There are multiple issues with the way the product handles URIs within certain schemes. The product does not warn the user that a dangerous navigation is about to take place. An attacker can manipulate the user interface so that the user’s action is interpreted as permission to proceed with opening a dangerous file. Because special characters in the URI are not sanitized, this could lead to the execution of arbitrary commands. An attacker can leverage this vulnerability to execute code in the context of the current user at medium integrity.
– Trend Micro’s Zero Day Initiative
Abdulrahman Al-Qabandi also shared a video as a Proof of Concept of the bug. You can check the video showing the bug in play below.
Via: Bleeping Computer







User forum
0 messages