NSA joins Microsoft in urging PC users to patch against Bluekeep
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
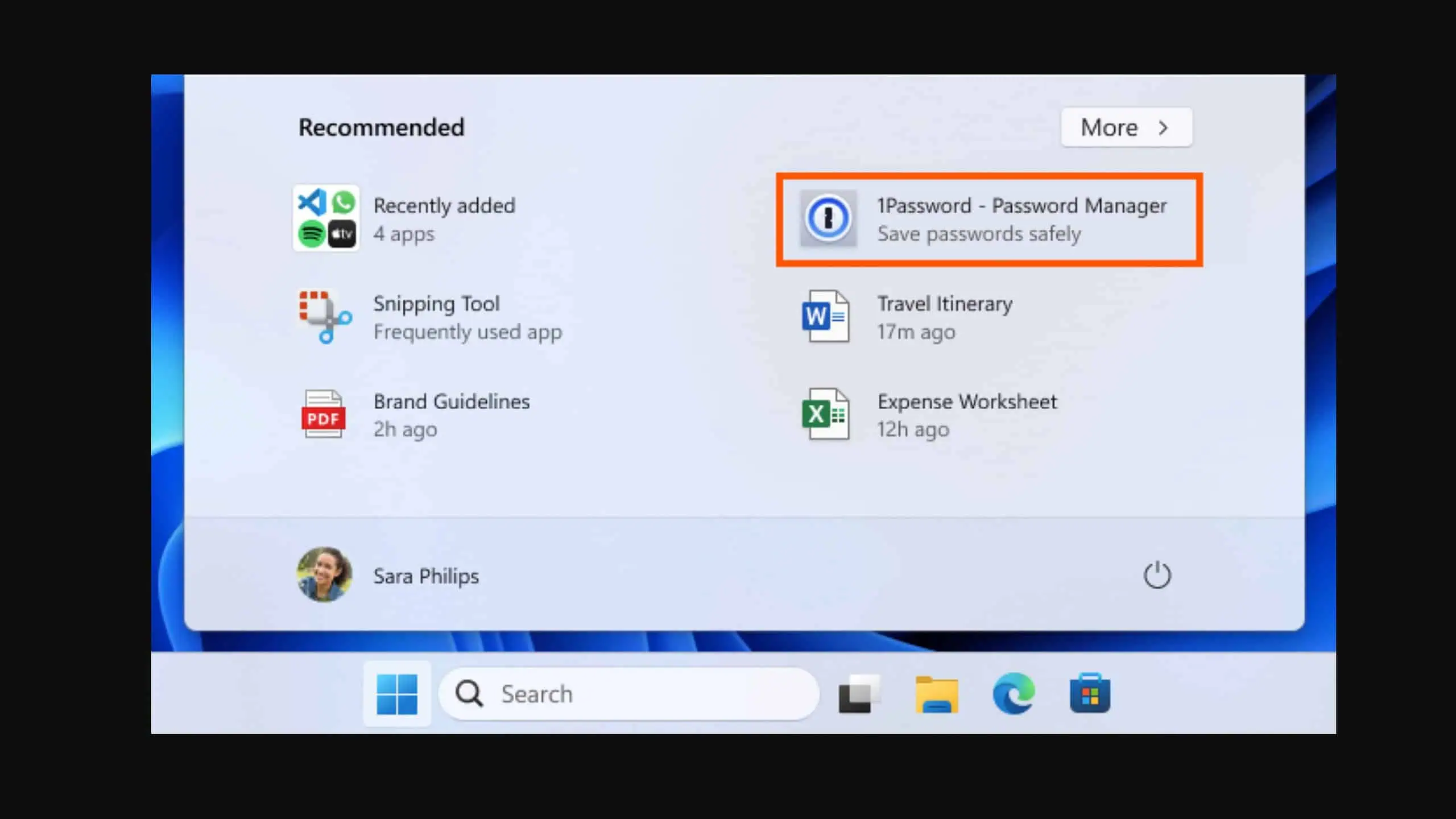
Last week Microsoft released a call to action, asking IT admins to urgently patch their devices against BlueKeep, a newly discovered exploit in the RDP service in Windows 7 and earlier, which could be easily wormable by hackers.
Simon Pope, director of incident response for the Microsoft Security Response Center said they were “confident that an exploit exists”, noting that it took 60 days between the patch for EternalBlue, the Wannacry vulnerability, and the actual Wannacry worm appearing.
Now the US National Security Agency (NSA) has added their voices, releasing an advisory, urging PC owners with older versions of Windows to patch their computers.
The advisory is part of an effort by the NSA to be more open about their concerns, in the wake of the Wannacry attack which used a vulnerability first discovered by the NSA and kept secret, and due to current waves of ransomware attacks which is crippling large institutions such as the Baltimore municipality.
On Twitter senior NSA adviser, Rob Joyce said some computer users could face a “significant risk” and should “patch and protect.”
NSA is raising their own concern that the Microsoft RDP flaw (#BlueKeep) is of significant risk to unpatched systems. Patch and protect! https://t.co/hj1c40psma
— Rob Joyce (@RGB_Lights) June 4, 2019
Security vendors Zerodium, McAfee, Kaspersky, Check Point, MalwareTech and Valthek, have all developed Proof of Concept exploits for BlueKeep, but are not releasing them.
Concerned Windows 7, Windows XP, Server 2003 and Server 2008 owners can read more about the remote code execution flaw in Remote Desktop Services at the bug reports at CVE-2019-0708, AKA BlueKeep here.
Via the BBC