Microsoft warns BlueKeep could be as bad as Wannacry
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
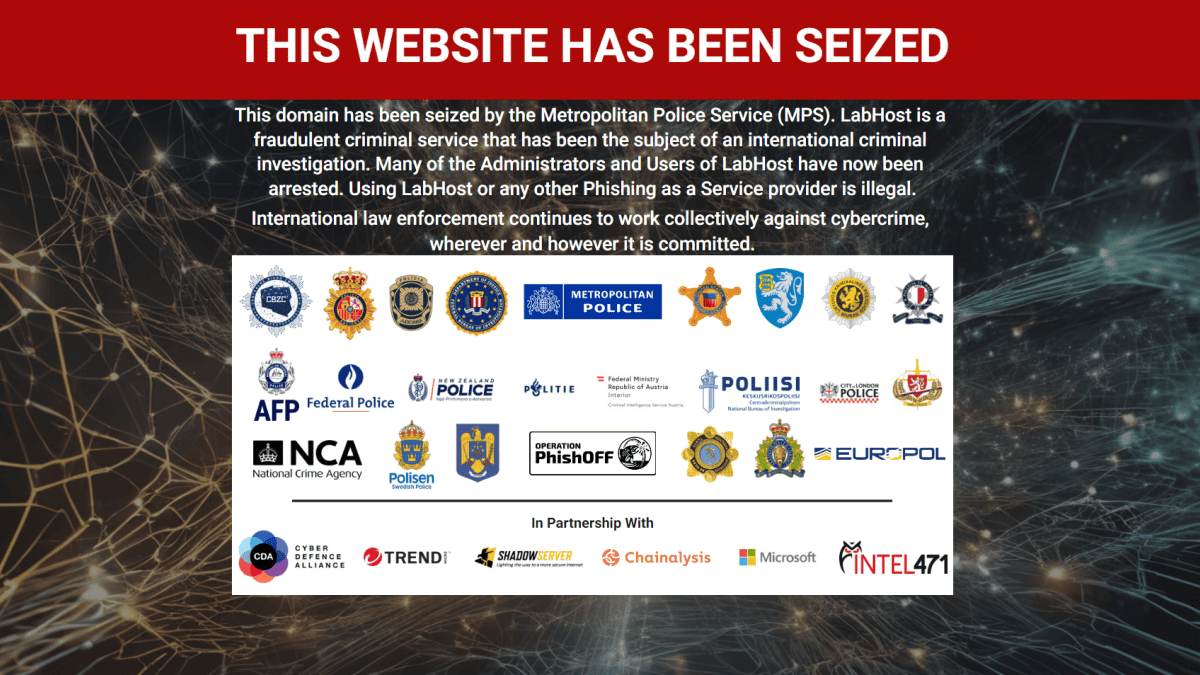
We reported two days ago that security researchers have estimated that there are still a million PCs in the wild vulnerable to Bluekeep, the RDP vulnerability in Windows XP, 7 and Server 2003 and Server 2008.
Now Microsoft has joined the call to action, asking IT admins to urgently patch their devices.
Simon Pope, director of incident response for the Microsoft Security Response Center said they were “confident that an exploit exists”, noting that it took 60 days between the patch for EternalBlue, the Wannacry vulnerability, and the actual Wannacry worm appearing.
“It’s been only two weeks since the fix was released and there has been no sign of a worm yet. This does not mean that we’re out of the woods,” Pope warns. “If we look at the events leading up to the start of the WannaCry attacks, they serve to inform the risks of not applying fixes for this vulnerability in a timely manner.”
Security vendors Zerodium, McAfee, Kaspersky, Check Point, MalwareTech and Valthek, have all developed Proof of Concept exploits for BlueKeep, but are not releasing them. A number of code samples have however been uploaded to GitHub, though these mostly appear to be trolls.
CVE-2019-0708, AKA BlueKeep, is a remote code execution flaw in Remote Desktop Services and affects Windows 7, Windows XP, Server 2003 and Server 2008. Microsoft is urged administrators to update impacted Windows systems as soon as possible.
Via BankInfoSecurity