New Excel vulnerability puts 120 million users at risk
3 min. read
Updated on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
Security researchers have found a new vulnerability in Microsoft Excel which can potentially put over 120 million users at risk. The vulnerability was discovered by researchers at the security firm Mimecast Services Ltd.
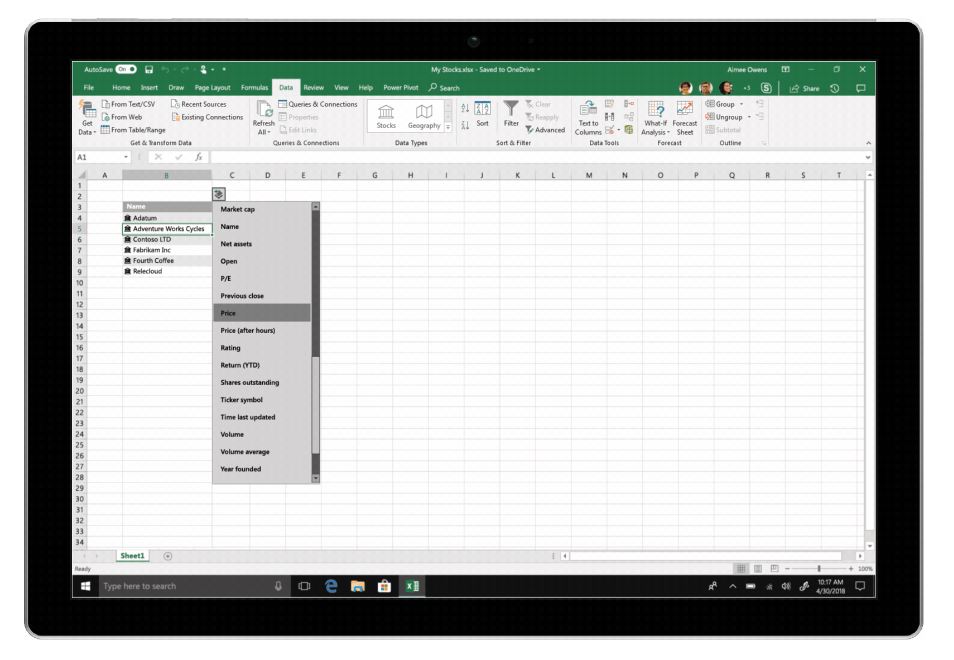
The vulnerability takes advantage of the Power Query function in Excel that allows users to pull data from other sources. Researchers at Mimecast Services Ltd published a blog post (via SiliconANGLE) explaining the vulnerability has how it can be exploited by hackers. The vulnerability will allow hackers to use Power Query to launch a remote Dynamic Data Exchange attack into an Excel spreadsheet. Not only that, but the vulnerability will also allow hackers to launch more sophisticated attacks involving malwares that can compromise the user’s machine as soon as the spreadsheet is opened.
The feature gives such rich controls that it can be used to fingerprint a sandbox or a victim’s machine even before delivering any payloads. The attacker has potential pre-payload and pre-exploitation controls and could deliver a malicious payload to the victim while also making the file appear harmless to a sandbox or other security solutions.
The good thing is that Microsoft already knows about the vulnerability and did release an advisory back in November 2017. The advisory noted that users will need to click through several security warnings in order to install malware onto their system. Microsoft also recommended users to disable DDE feature when not in use to block external data connections.
Mimecast strongly recommends all Microsoft Excel customers implement the workarounds suggested by Microsoft as the potential threat to these Microsoft users is real and the exploit could be damaging.
The good thing is that there’s no report of the vulnerability being exploited in the wild. The bad news, however, is that the DDE feature is usually enabled by default and users might not turn it off when not in use. Meni Farjon, the chief scientist at Mimecast, noted that it’s unclear how many organizations are following Microsoft’s earlier advice, saying that “it is unlikely that many organizations have disabled it.”
As of now, Microsoft has just released an advisory and is relying on users to take appropriate actions. The wise thing to do right now is to disable the DDE feature and don’t download and open spreadsheets sent over emails. Last but not least, make sure you don’t ignore any security prompts by Excel as those might be warning you about potential malware.







User forum
0 messages