Microsoft assisting Ukrainian government in fighting off Russian cyber-attack
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
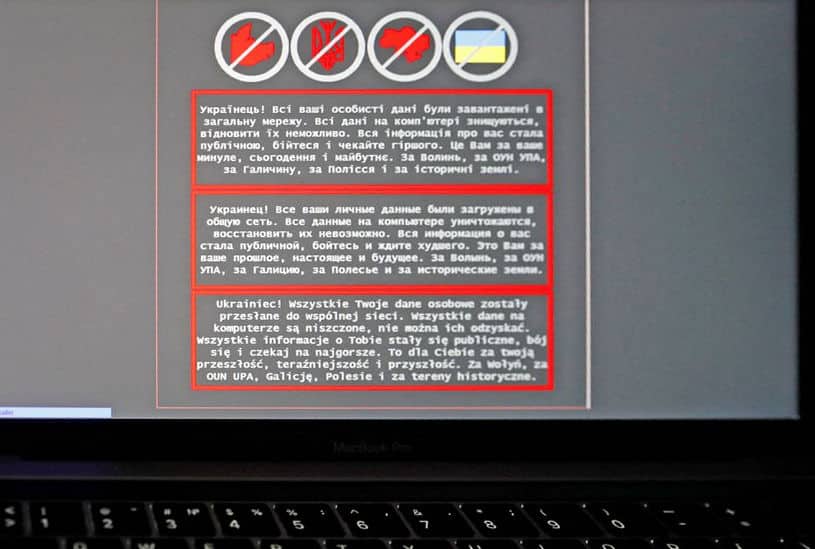
Microsoft has yesterday confirmed reports of a cyber-attack on the Ukrainian government and their ancillary organizations.
Microsoft first detected this malware on January 13 2022 in systems belonging to several Ukrainian government agencies and organizations that work closely with the Ukrainian government. The malware is disguised as ransomware but, if activated by the attacker, would render the infected computer system inoperable. Fortunately, it does not appear these attacks utilize any vulnerability in Microsoft products and services.
The organizations affected by this malware include government agencies that provide critical executive branch or emergency response functions and an IT firm that manages websites for public and private sector clients, including government agencies whose websites were recently defaced.
The attack occurred soon after failed security talks between Ukraine and Russia after more than 100,000 Russian troops started massing on Ukraine’s borders.
Microsoft has notified each of the impacted organizations they have identified so far and has partnered with other cybersecurity providers to share information, notified appropriate government agencies and say they will continue to work with the cybersecurity community to identify and assist targets and victims.
Microsoft has also built and deployed protections for this malware into Microsoft 365 Defender Endpoint Detection (EDR) and Anti-virus (AV) protections wherever these products are deployed, both on-premises and in the cloud.
The Microsoft Threat Intelligence Center (MSTIC) has published a technical blog post detailing Microsoft’s ongoing investigation and how the security community can detect and defend against this malware. So far they have not noticed the fingerprint of groups they have previously tracked in these attacks.
Read all the technical detail at Microsoft here.







User forum
0 messages