Security Researcher demonstrates Thunderspy, an undetectable hardware attack which disables all Thunderbolt security
3 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
We have heard recently that Microsoft was not a fan of Thunderbolt as they consider that it offers insecure direct access to a PC’s RAM, which could lead to all kinds of shenanigans.
Now security researcher Björn Ruytenberg has demonstrated an undetectable and rapid hardware attack which easily bypasses Intel’s Thunderbolt security features and which allows an attacker to copy memory from a locked and encrypted PC for example or easily bypass the lock screen.
He showed off a tool called Thunderspy which takes advantage of the following vulnerabilities:
- Inadequate firmware verification schemes
- Weak device authentication scheme
- Use of unauthenticated device metadata
- Downgrade attack using backwards compatibility
- Use of unauthenticated controller configurations
- SPI flash interface deficiencies
- No Thunderbolt security on Boot Camp
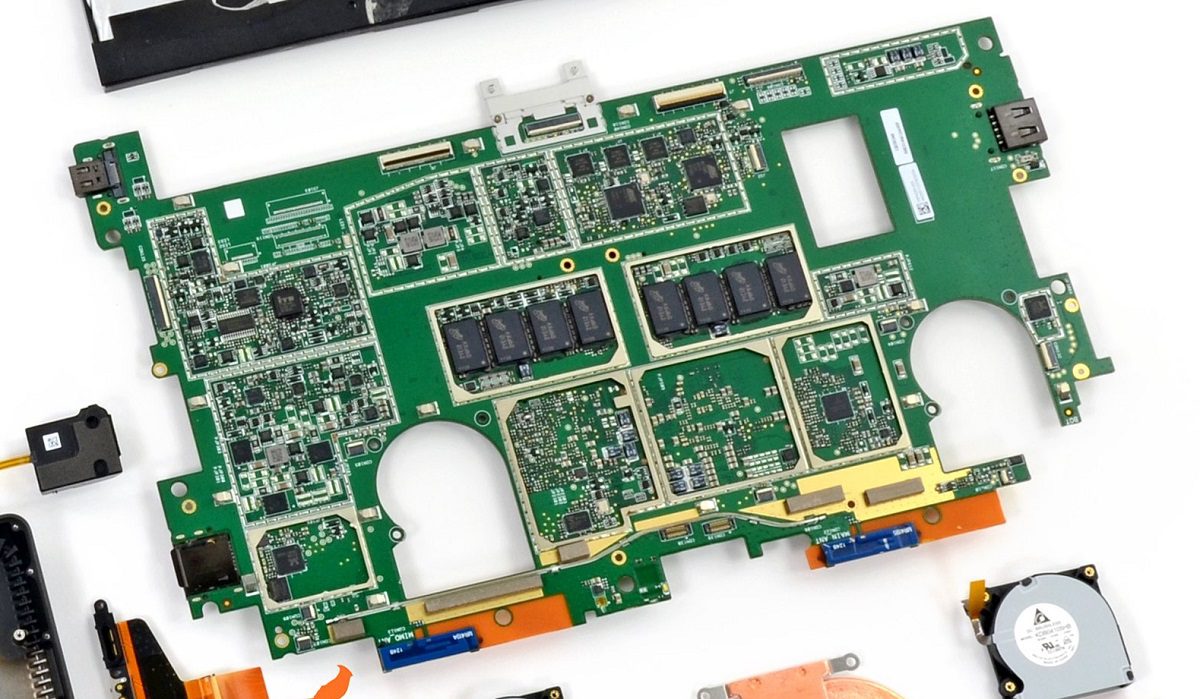
The tool allows attackers with physical access to your PC to permanently reprogram your Thunderbolt controller and from then on allow anyone direct memory access without any security measures, Microsoft’s nightmare scenario.
Ruytenberg demonstrates the attack in the video below:
His tool allows the ability to create arbitrary Thunderbolt device identities, clone user-authorized Thunderbolt devices, and finally obtain PCIe connectivity to perform DMA attacks. In addition, it allows unauthenticated overriding of Security Level configurations, including the ability to disable Thunderbolt security entirely, and restoring Thunderbolt connectivity if the system is restricted to exclusively passing through USB and/or DisplayPort, and finally, permanently disable Thunderbolt security and block all future firmware updates.
Ruytenberg notes that all Thunderbolt-equipped systems shipped between 2011-2020 are vulnerable. Some systems providing Kernel DMA Protection, shipping since 2019, are partially vulnerable.
The Thunderspy vulnerabilities cannot be fixed in software, and will impact future standards such as USB 4 and Thunderbolt 4, and will ultimately require a silicon redesign.
On newer PCs (2019 onwards) Intel’s Kernel DMA Protection offers some protection, but interestingly when Apple MacOS laptops boot into Bootcamp all Thunderbolt security is disabled.
Ruytenberg is providing an open-source tool, Spycheck, that verifies whether your systems are vulnerable to Thunderspy. If it is found to be vulnerable, Spycheck will guide users to recommendations on how to help protect their system.
If you have an affected system, Ruytenberg suggests:
- Connect only your own Thunderbolt peripherals. Never lend them to anybody.
- Avoid leaving your system unattended while powered on, even when screenlocked.
- Avoid leaving your Thunderbolt peripherals unattended.
- Ensure appropriate physical security when storing your system and any Thunderbolt devices, including Thunderbolt-powered displays.
- Consider using hibernation (Suspend-to-Disk) or powering off the system completely. Specifically, avoid using sleep mode (Suspend-to-RAM).
Check out the full write-up at Ruytenberg’s site here.
It has always been a truism that if an attacker has physical access to your PC it is essentially game-over, though it seems Microsoft does take even this scenario seriously when designing their Surface products. Does this news change our reader’s views on the importance of having a very versatile port like Thunderbolt on your PC? Let us know below.








User forum
0 messages