Massive security hole lets attackers use Cortana to run Powershell scripts from above the lock screen
There is such a thing as being too helpful, especially when you are helping people with nefarious intent.
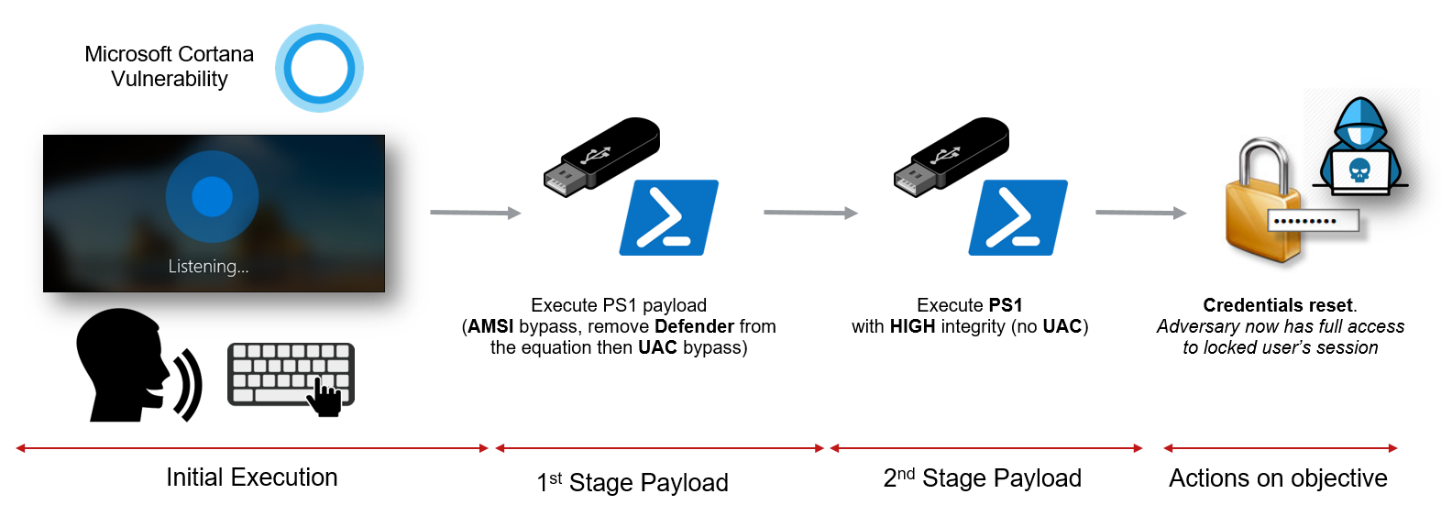
So it is with Cortana on Windows 10, which security researchers have discovered is all too happy to run Powershell commands from above the lock screen, which would enable attackers to do nearly anything, including for example resetting your password and logging into your PC by simply having physical access to your PC, even if it is locked and encrypted.
The trick is pretty simple, as described my McAfee.
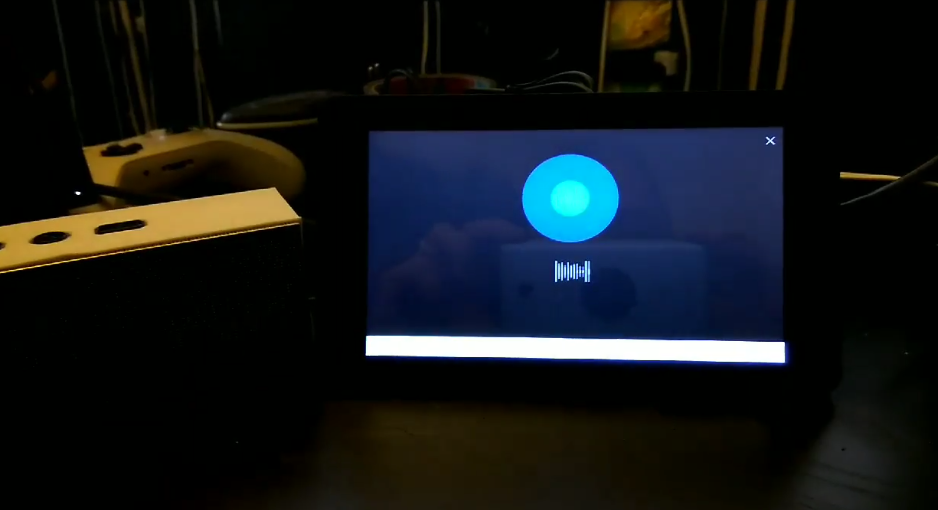
- Trigger Cortana via “Tap and Say” or “Hey Cortana”
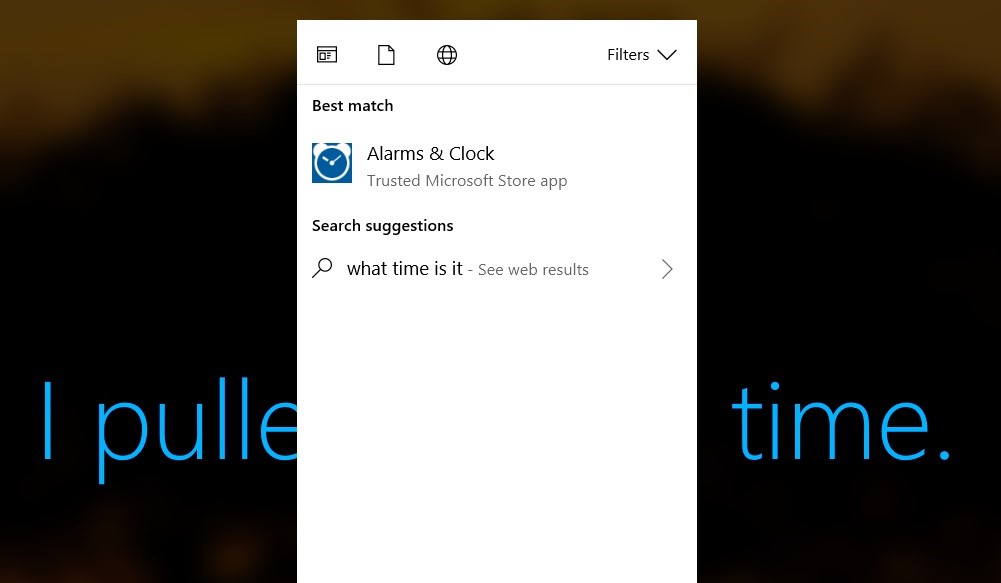
- Ask a question (this is more reliable) such as “What time is it?”
- Press the space bar, and the context menu appears
- Press esc, and the menu disappears
- Press the space bar again, and the contextual menu appears, but this time the search query is empty
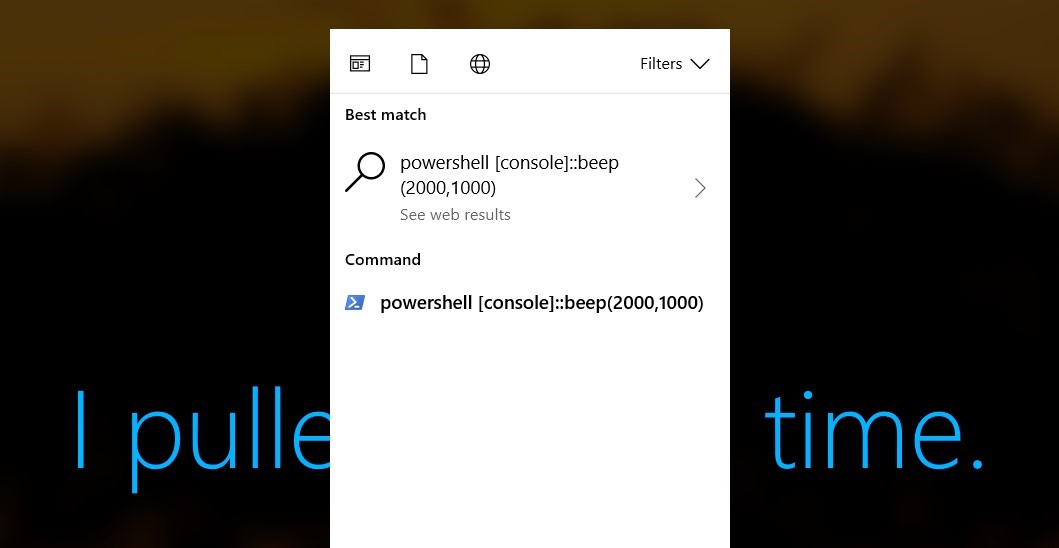
- Start typing (you cannot use backspace). If you make a mistake, press esc and start again.
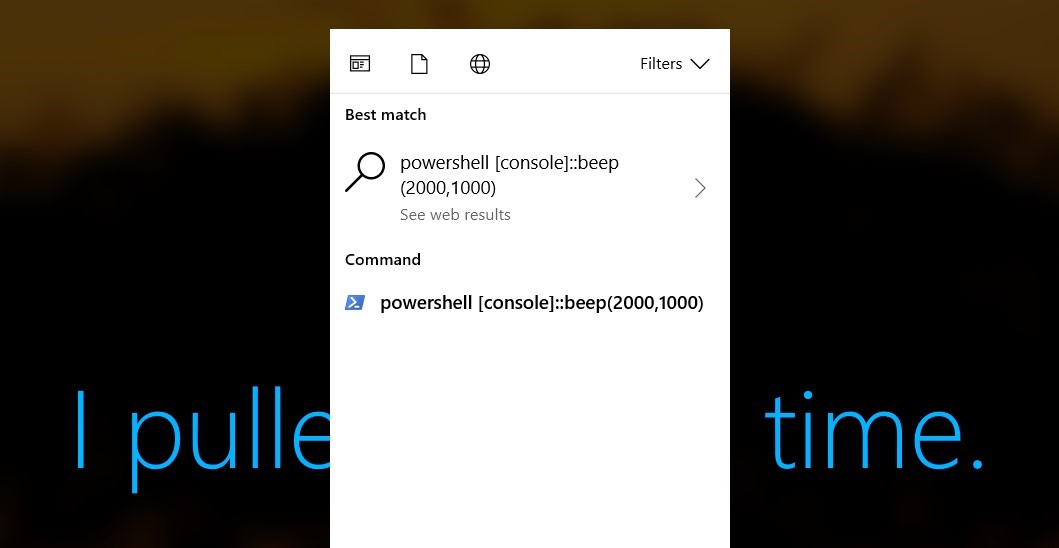
- When done (carefully) typing your command, click on the entry in the Command category. (This category will appear only after the input is recognized as a command.)
- You can always right click and select “Run as Administrator” (but remember the user would have to log in to clear the UAC)
Besides executing arbitrary commands Cortana will also leak confidential information, such as the content of files, from above the lock screen.
McAfee has already informed Microsoft of the issue some months ago, and Microsoft has released a fix with the June 2018 cumulative update (as part of CVE-2018-8140), but we assume many enterprise PCs will remain vulnerable for some time as patches roll out slowly.
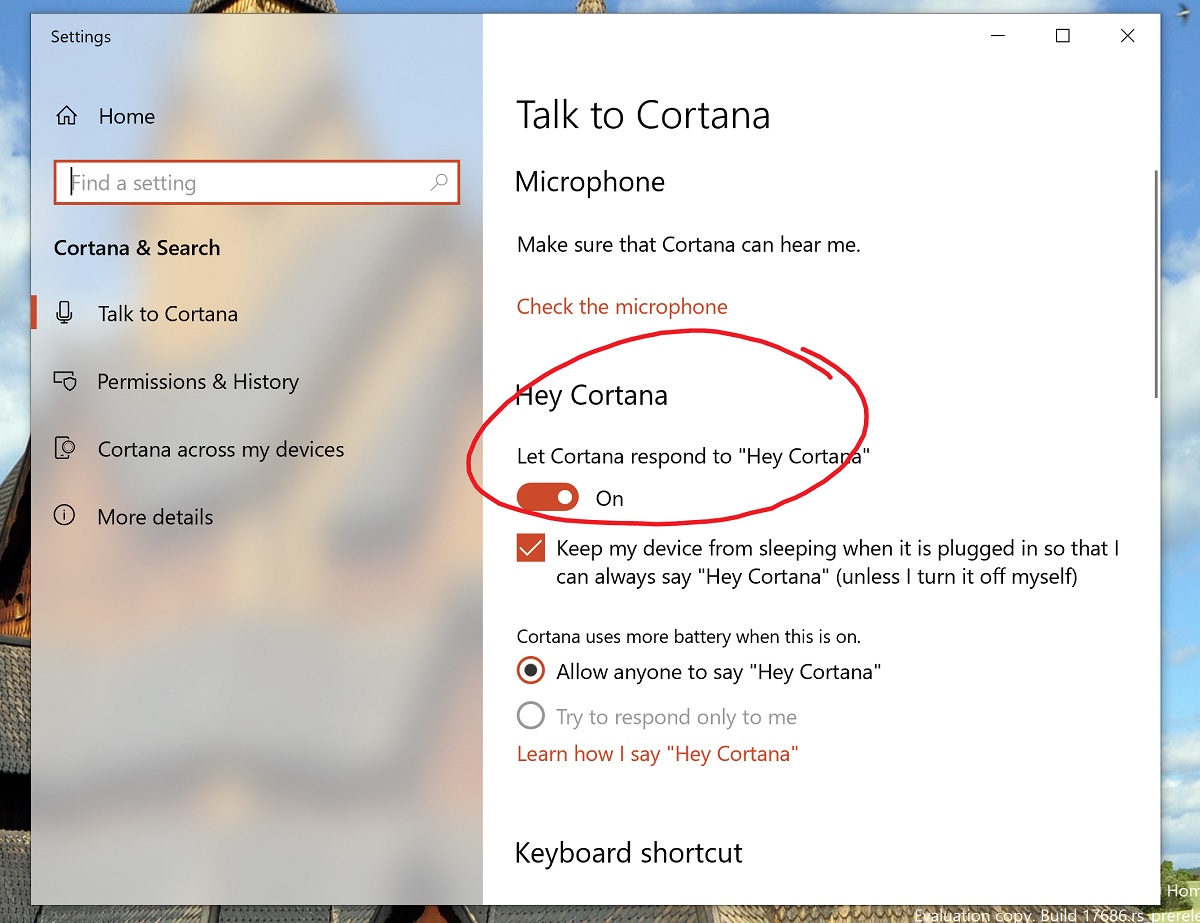
Part of the issue is that Hey Cortana is enabled by default, making Windows 10 users uniformly vulnerable to above lock screen attacks and information leakage. McAfee recommends the best fix is to disable this feature unless you actually use it, which can be done in Cortana Search and Settings menu in the Settings app.
Read all the gory details at McAfee here.
via WindowsLatest
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more







User forum
0 messages