Apple's AirTag tracker hacked and reprogrammed
1 min. read
Updated on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more

A hacker has managed to access the programming interface for Apple’s Airtag tracker and reprogram it with new information.
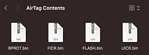
Hacker stacksmashing managed to break into the microcontroller of the Airtag and extract and then reprogram the firmware of the device.
His first demonstration was altering the data transmitted by the NFC chip in the device, as can be seen in his video below:
Built a quick demo: AirTag with modified NFC URL ?
(Cables only used for power) pic.twitter.com/DrMIK49Tu0
— stacksmashing (@ghidraninja) May 8, 2021
The hack also demonstrates a threat model brought on by the hack. Similar to leaving a “lost” USB device in front of a company, a hacker could leave a “lost” set of keys or wallet with a reprogrammed Airtag in the lobby of a company, with a reasonable expectation an employee of the company would scan it, and potentially have their iPhone compromised as the first step for a wider attack.
At present, the full capability delivered by the hack is not known yet, but given how popular the AirTags already are I expect we will hear a lot more very soon.
via Engadget










User forum
0 messages