Study: Majority of zero-day vulnerabilities now failed against Windows 10
1 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more

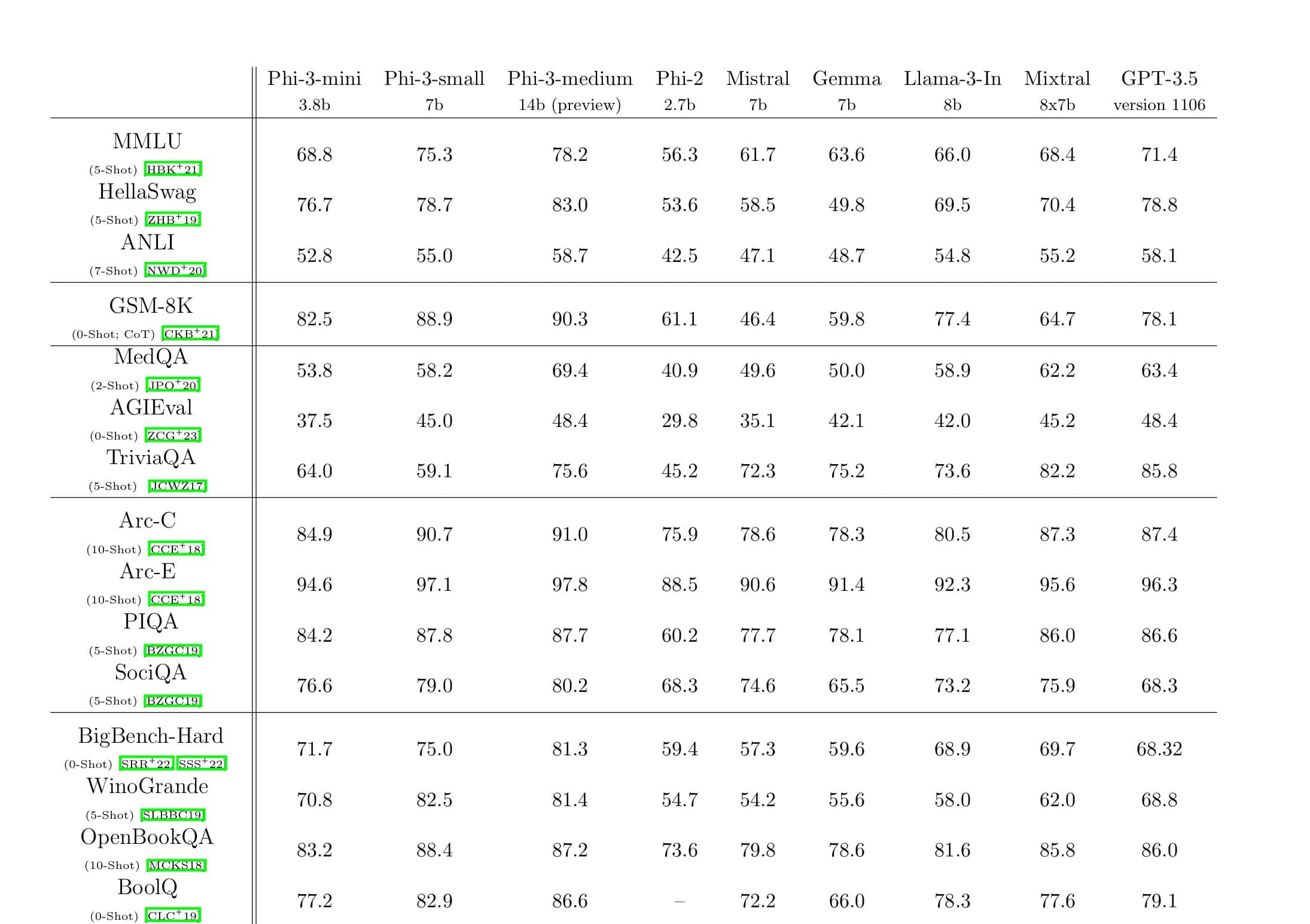
Microsoft has proved their latest operating system is the safest around; with only 40% of all Windows zero-days successfully exploited against the latest Windows versions since 2015.
Matt Miller, security engineer with the Microsoft Security Response Centre, analysed zero-day exploitation attempts between 2015 and 2019.
Back in February, Miller gave a talk at the BlueHat Israel security conference. He showed that Windows vulnerabilities are mostly exploited before a patch is released or when a patch fails months after.
Thanks to Control Flow Guard and Device Guard security systems, amongst others, users with an updated OS are mostly safeguarded. In two out of three cases, the zero-days didn’t work against recent versions of Windows because of the mitigations added to the OS.
Additionally, his findings show that 70% of all security bugs addressed by Microsoft in the past 12 years were memory management-related issues.
Miller’s MSRC colleagues are currently exploring Rust as an alternative to C and C++. The language’s security features could cause a reduction in the number of memory-related bugs.
So with these statistics in mind, it seems that attackers are better off keeping zero-days attacks to older Windows versions.
Read more about the exploit and Microsoft’s mitigation measures here.
Source: zdnet