Microsoft's Cloud App Security feature offers immediate logoff for suspicious users
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
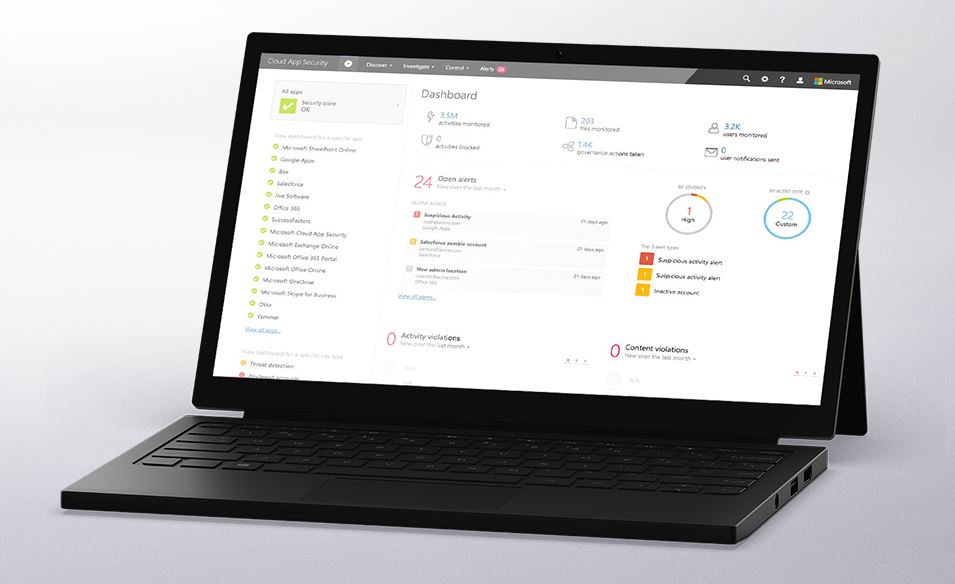
Cloud App Security allows organizations to take full advantage of cloud applications, but keep their data in control, through improved visibility into activity. It also helps them uncover shadow IT, assess risk, enforce policies, investigate activities, and stop threats. One of the main challenges in protecting cloud based apps is that attackers can move quickly to access critical data. With the integration of Azure Active Directory, Microsoft today announced new feature in Cloud App Security that will help admins respond immediately.
When an attacker gains unauthorized access to an account, a common industry practice is to disable the account. But this is not enough! If the account is actively being used to exfiltrate data, gain elevated privileges in the organization, or any other method that keeps the attacker’s session active, they can still use the compromised account.
When a suspicious activity is identified in Cloud App Security portal, admins can now initiate an auto-remediation action logging off these users. Cloud App Security invalidates all the user’s refresh tokens issued to cloud apps. Users need to sign in again to Office 365 and all other apps accessed through Azure Active Directory.
Admins can learn about how to enable this feature here.









User forum
0 messages