Microsoft Windows MotW flaw is being exploited in the wild; free micropatch is available via 0patch
3 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more

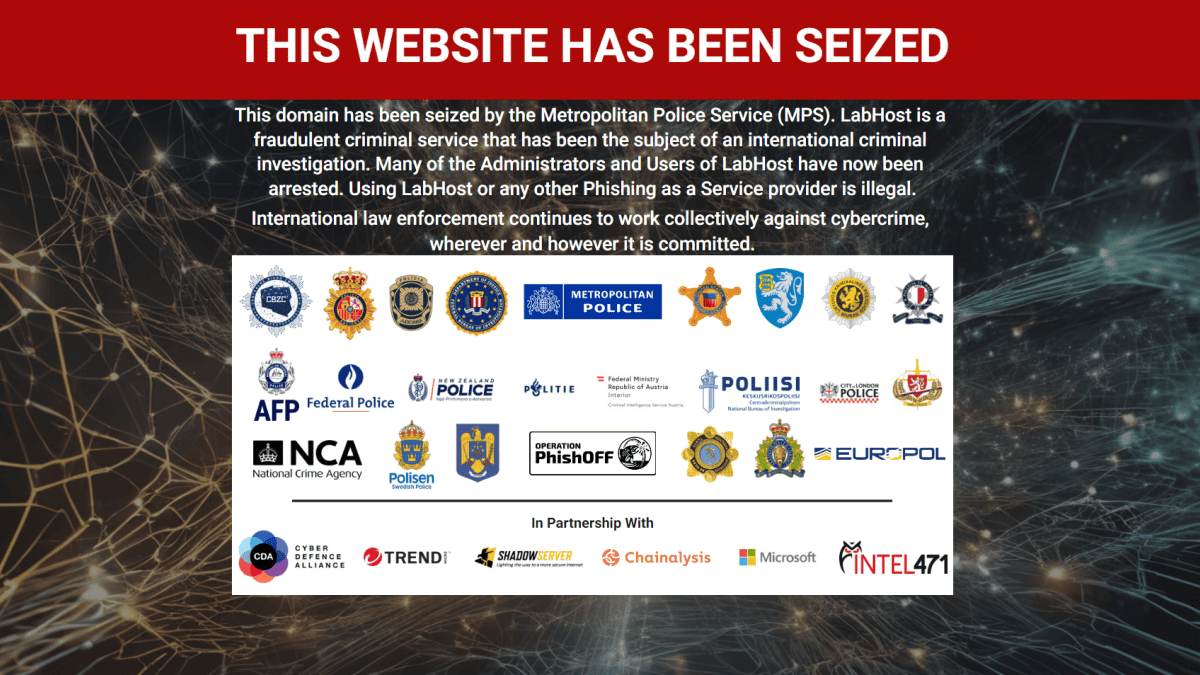
A zero-day flaw in the Windows Mark of the Web (MotW) labels is being actively exploited by attackers. MotW is known for being applied to extracted ZIP archive files, executables, and docs originating from untrusted places on the web. (via Bleeping Computer)
So if it were a ZIP instead of ISO, would MotW be fine?
Not really. Even though Windows tries to apply MotW to extracted ZIP contents, it's really quite bad at it.
Without trying too hard, here I've got a ZIP file where the contents retain NO protection from Mark of the Web. pic.twitter.com/1SOuzfca5q— Will Dormann (@wdormann) July 5, 2022
The labels serve as a layer of protection and security mechanism that warns your system, including other programs and apps, of possible threats and malware if a specific file is installed. Thus, with attackers preventing the application of the MotW labels, warning signals won’t be executed, leaving users oblivious to the threats a file might have. Thankfully, although there is still no official fix from Microsoft regarding this issue, 0patch is offering one you can obtain now.
“Attackers therefore understandably prefer their malicious files not being marked with MOTW; this vulnerability allows them to create a ZIP archive such that extracted malicious files will not be marked,” writes 0patch Co-founder and ACROS Security CEO Mitja Kolsek in a post explaining the nature of MotW as an important security mechanism in Windows. “An attacker could deliver Word or Excel files in a downloaded ZIP that would not have their macros blocked due to the absence of the MOTW (depending on Office macro security settings), or would escape the inspection by Smart App Control.”
The issue was first reported by a senior vulnerability analyst at IT solution company Analygence named Will Dormann. Interestingly, Dormann first introduced the problem to Microsoft in July, but despite having the report read by August, a fix is still unavailable for every Windows user affected.
Almost the same response was encountered by the earlier issue uncovered by Dormann in September, where he discovered Microsoft’s out-of-date vulnerable driver blocklist, resulting in users being exposed to malicious drivers since 2019. Microsoft didn’t officially comment on the issue, but project manager Jeffery Sutherland participated in Dormann’s series of tweets this October, saying solutions are already available to address the issue.
As of now, reports are saying the MotW flaw is still being exploited in the wild, while Microsoft is still mum about the plans on how it will resolve it. Nevertheless, 0patch is offering free patches that can serve as temporary alternatives for different Windows systems affected until a Microsoft solution arrives. In the post, Kolsek says the patch covers systems of Windows 11 v21H2, Windows 10 v21H2, Windows 10 v21H1, Windows 10 v20H2, Windows 10 v2004, Windows 10 v1909, Windows 10 v1903, Windows 10 v1809, Windows 10 v1803, Windows 7 with or without ESU, Windows Server 2022, Windows Server 2019, Windows Server 2016, Windows Server 2012, Windows Server 2012 R2, and Windows Server 2008 R2 with or without ESU.
For current 0patch users, the patch is already available on all online 0patch Agents. Meanwhile, those new to the platform can create a free 0patch account to register a 0patch Agent. The patch application is said to be automatic, and no reboot is needed.