Microsoft warns public of ongoing click fraud campaign seen in ads, YouTube comments
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more

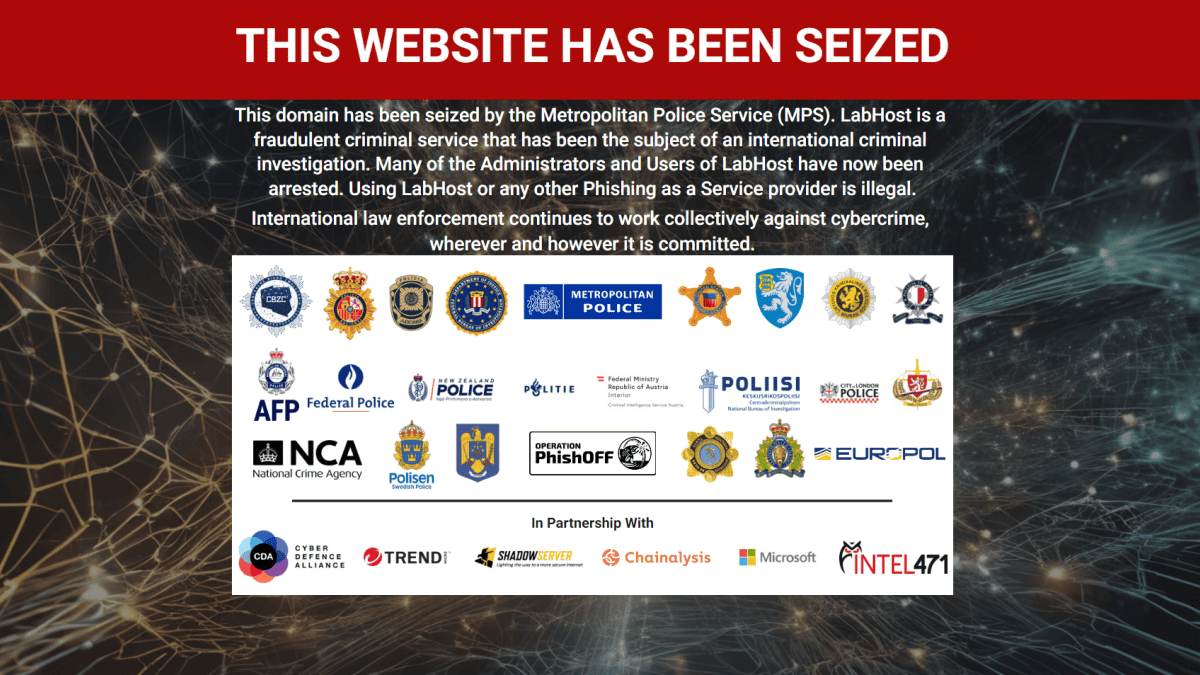
Microsoft warned the public of a wide-ranging click fraud campaign, which it attributes to a threat actor tracked as DEV-0796. According to the company, the attackers can monetize the clicks generated by a browser node-webkit or malicious browser extension installed on devices without the users’ knowledge.
The tech giant explained in a tweet that the campaign victimizes unknowing users when they click malicious ads or YouTube comments. Doing so will download an ISO file pretending to be game cheats, which, when opened, will install the browser node-webkit (NW.js) or a browser extension that the threat actors need. Microsoft added that they observed the actors using DMG files, an Apple Disk Image file, which means the campaign reflects a multi-platform activity.
“To protect against this threat, Microsoft highly recommends customers to turn on PUA protection to block the installation of malicious and unwanted programs, and use Defender SmartScreen to block access to malicious download sites and attacker-controlled servers,” suggested Microsoft in a tweet. “Microsoft 365 Defender customers can also refer to the threat analytics article that we published about this threat. The report contains technical details, IOCs, mitigation guidance, and hunting queries that can enable organizations to locate and respond to related activity.”
The news is not surprising anymore as threat actors commonly find gamers fine targets in their campaigns, especially those desperately looking for free cheats online. Earlier in September, a report from endpoint security vendor and consumer IT security software company Kaspersky showed how widespread malware distribution is through different famous game titles. Topping the list is Minecraft, which affected 131,005 users from July 2021 through June 2022 using the 23,239 files distributed.