Microsoft warns of Adrozek adware attack
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more

Microsoft has issued an advisory about a concerted push to spread Adrozek, a new piece of adware which is being distributed by large, well organized threat actors.
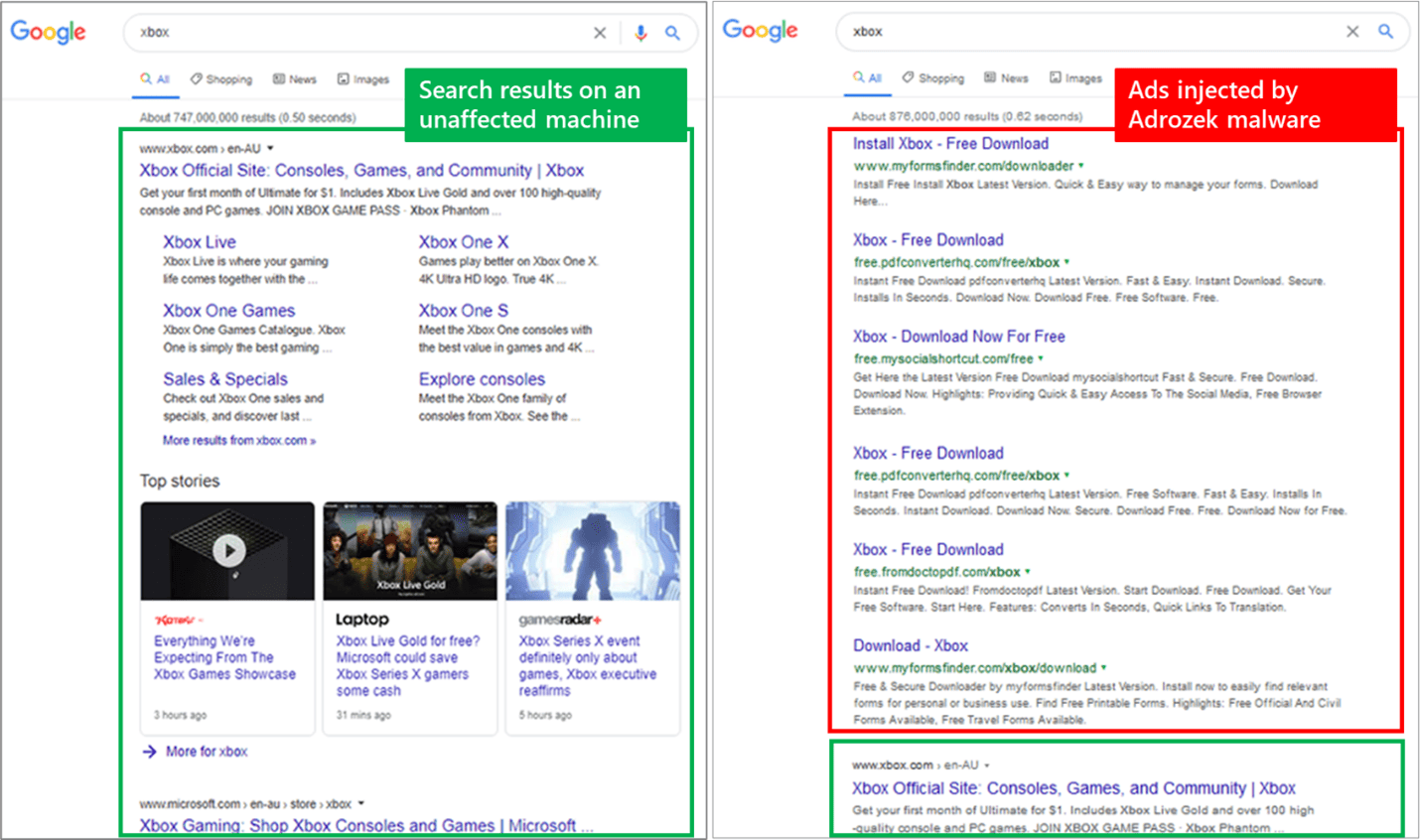
Microsoft warns the browser modifier “adds browser extensions, modifies a specific DLL per target browser, and changes browser settings to insert additional, unauthorized ads into web pages.”
The malware is being spread by 159 unique domains and Microsoft notes:
The intended effect is for users, searching for certain keywords, to inadvertently click on these malware-inserted ads, which lead to affiliated pages. The attackers earn through affiliate advertising programs, which pay by amount of traffic referred to sponsored affiliated pages.
Microsoft says besides adding extra ads to your search results, the Adrozek also tries to steal your browser credentials.
Microsoft says between May to September 2020, they recorded hundreds of thousands of encounters of the Adrozek malware across the globe, with heavy concentration in Europe and in South Asia and Southeast Asia.
The Adrozek malware is installed on devices through drive-by download and each download is heavily obfuscated, to attempt to evade detection. Once in your PC it makes changes to certain browser extensions. On Google Chrome, the malware typically modifies “Chrome Media Router”, one of the browser’s default extensions, but different extensions have also been involved. It then connects to the attacker’s server to fetch additional scripts, which are responsible for injecting advertisements into search results.
It also attempts to modify browser security settings to attempt to remain undetected and turns off automatic updates for the browser.
Microsoft notes these complex behaviors, and the fact that the campaign uses polymorphic malware, require protections that focus on identifying and detecting malicious behaviour and that Microsoft Defender Antivirus, the built-in endpoint protection solution on Windows 10, uses behaviour-based, machine learning-powered detections that can block Adrozek.
Read more about Androzek at Microsoft here.
via DarkReadings