Microsoft warns of a massive and resurgent Emotet phishing campaign to steal banking info
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
Companies and individuals should be high alert after Microsoft warned of a massive malware campaign targeting end-user banking details.
Microsoft reports tens of thousands of emails with hundreds of unique attachments are being sent to users as part of a new campaign using the Emoter malware.
The Emotet banking Trojan was first identified by security researchers in 2014. Emotet was originally designed as a banking malware that attempted to sneak onto your computer and steal sensitive and private information. Later versions of the software saw the addition of spamming and malware delivery services—including other banking Trojans.
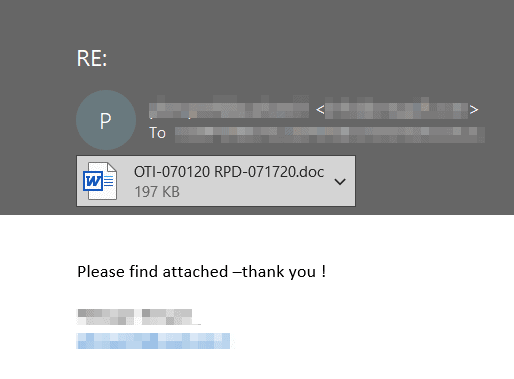
Microsoft reports the phishing campaign had been silent for months but has recently returned in force. The new campaign uses longtime Emotet tactics: emails carrying links or documents with highly obfuscated malicious macros that run a PowerShell script to download the payload from 5 download links. The download URLs typically point to compromised websites, characteristic of Emotet operations.
Emotet uses functionality that helps the software evade detection by some anti-malware products. Emotet uses worm-like capabilities to help spread to other connected computers. This helps in the distribution of malware. This functionality has led the Department of Homeland Security to conclude that Emotet is one of the most costly and destructive malware, affecting government and private sectors, individuals and organizations, and costing upwards of $1M per incident to clean up.
Microsoft, of course, notes that Microsoft Threat Protection’s coordinated defence caught this campaign and that Office 365 ATP provides durable detections of malicious attachments and URLs in emails and that Microsoft Defender ATP blocks malicious components on endpoints.
Read more about Emotet and its mitigation at Microsoft here.







