Microsoft says PrintNightmare is already being exploited, offers workaround
3 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more

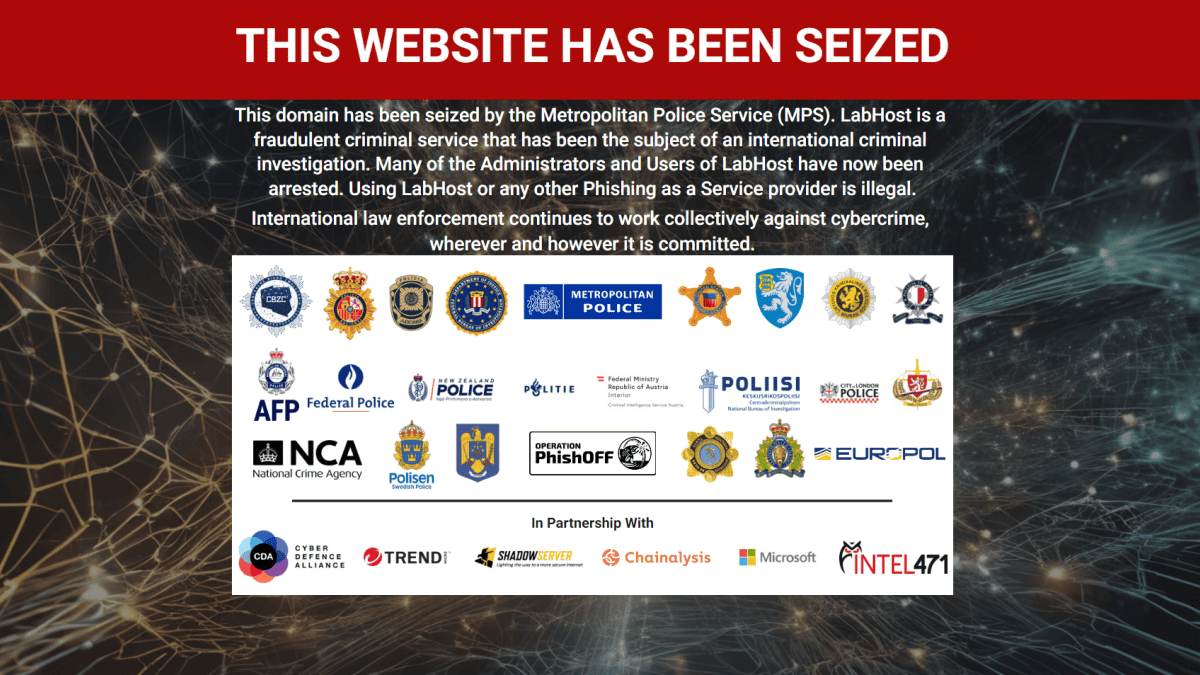
We reported two days ago on a new and unpatched Zero-day exploit that has just been released which grants attackers full Remote Code Execution capabilities on fully patched Windows Print Spooler devices.
The hack, called PrintNightmare, allows attacker code to run with full system privileges and was released along with Proof of Concept code, so was ripe to be exploited by hackers.
The main mitigating factor is that hackers need some (even low-privilege) credentials for the network, but for enterprise networks, these can be easily purchased for around $3.
Microsoft has now finally responded to the news by posting the CVE-2021-34527 Windows Print Spooler Remote Code Execution Vulnerability advisory.
Microsoft says:
Microsoft is aware of and investigating a remote code execution vulnerability that affects Windows Print Spooler and has assigned CVE-2021-34527 to this vulnerability. This is an evolving situation and we will update the CVE as more information is available.
A remote code execution vulnerability exists when the Windows Print Spooler service improperly performs privileged file operations. An attacker who successfully exploited this vulnerability could run arbitrary code with SYSTEM privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
An attack must involve an authenticated user calling RpcAddPrinterDriverEx().
Please ensure that you have applied the security updates released on June 8, 2021, and see the FAQ and Workaround sections in this CVE for information on how to help protect your system from this vulnerability.
In their Exploitability Assessment, they note that they have already detected exploits.
Microsoft offers the following workaround, which however disables your Print Spooler:
Determine if the Print Spooler service is running (run as a Domain Admin)
Run the following as a Domain Admin:
Get-Service -Name SpoolerIf the Print Spooler is running or if the service is not set to disabled, select one of the following options to either disable the Print Spooler service, or to Disable inbound remote printing through Group Policy:
Option 1 – Disable the Print Spooler service
If disabling the Print Spooler service is appropriate for your enterprise, use the following PowerShell commands:
Stop-Service -Name Spooler -Force
Set-Service -Name Spooler -StartupType DisabledImpact of workaround Disabling the Print Spooler service disables the ability to print both locally and remotely.
Option 2 – Disable inbound remote printing through Group Policy
You can also configure the settings via Group Policy as follows:
Computer Configuration / Administrative Templates / Printers
Disable the “Allow Print Spooler to accept client connections:” policy to block remote attacks.
Impact of workaround This policy will block the remote attack vector by preventing inbound remote printing operations. The system will no longer function as a print server, but local printing to a directly attached device will still be possible.
Read all the details at Microsoft here.