Huge security flaws found in Apple iOS devices
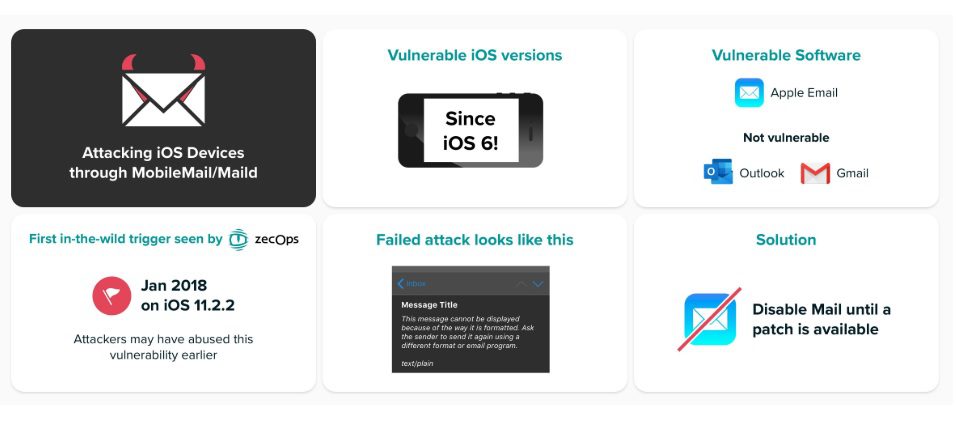
Two new serious security vulnerabilities in Apple iOS operating system were revealed today. These vulnerabilities allow attackers to gain access to an iOS device without any user action. Generally, when a user clicks some link or installs some application, the vulnerability will be exploited. But in this case, the attacker can just send emails that consume a significant amount of memory and get remote code execution capabilities in the device. According to security firm Zecops, attackers are already using these vulnerabilities in the wild targeting the following:
- Individuals from a Fortune 500 organization in North America
- An executive from a carrier in Japan
- A VIP from Germany
- MSSPs from Saudi Arabia and Israel
- A Journalist in Europe
- Suspected: An executive from a Swiss enterprise
All devices running iOS 6 and above are affected by these security flaws. In the recent iOS versions, the attack can be carried out by the below ways:
- Attack on iOS 13: Unassisted (/zero-click) attacks on iOS 13 when Mail application is opened in the background
- Attack on iOS 12: The attack requires a click on the email. The attack will be triggered before rendering the content. The user won’t notice anything anomalous in the email itself
- Unassisted attacks on iOS 12 can be triggered (aka zero click) if the attacker controls the mail server
Apple is aware of these security flaws in iOS and will be releasing an update soon to fix these. If you want to prevent such attacks until Apple releases an update, you need to avoid using the Apple mail app. Instead, you can use the Microsoft Outlook app or other similar email clients.
You can learn more about these vulnerabilities from the source link below.
Source: Zecops
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more







User forum
0 messages