Benchmark tests detail impact of Microsoft's Meltdown and Spectre Windows 10 patch
3 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
With proof of concept exploits already in the wild it seems a very good idea to update your PC as rapidly as possible, but today we have already seen some sites explaining how to disable automatic updates due to the rumoured performance impacts of the patch, which has been said to reduce execution speed by up to 30%.
Intel has, however, said for most tasks performance impact should be minimal, and now Techspot has done some benchmark tests to see exactly who will be affected.
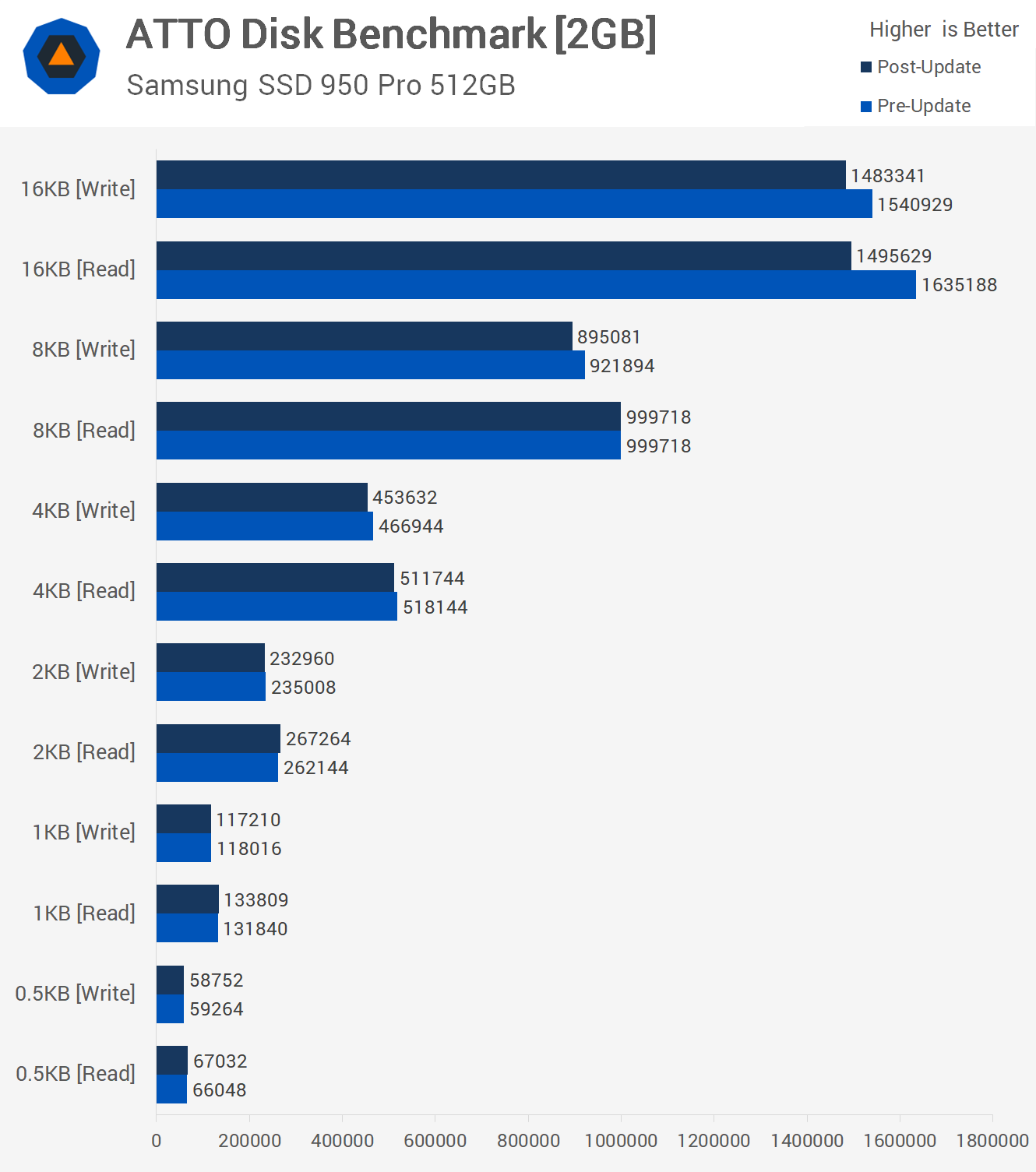
First, the bad news.
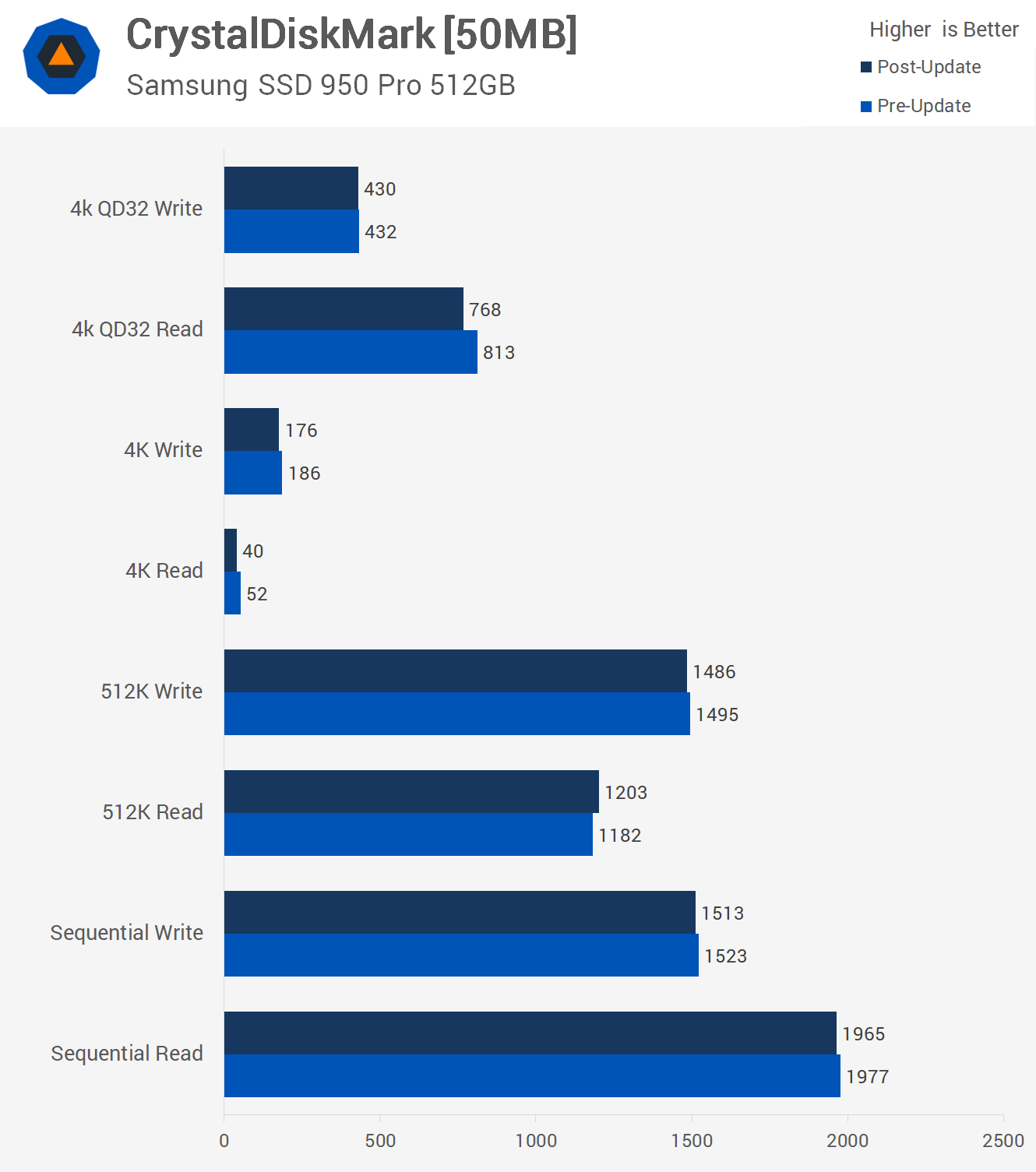
In other operations with larger files impact appears to be minimal to non-existent.
On the other hand, the good news is that there is little to no impact on other tasks, and even some improvement following the patch.
For 3D rendering, the Cinebench R15 multi-threaded score was reduced by 2% while the single thread score was increased by a percent, a likely non-significant result. Results for the Blender and Corona benchmark was also within the margin of error.
For productivity, Excel and 7-Zip benchmarks were near identical as was Veracrypt.
For gamers, Ashes of the Singularity was actually slightly faster following the patch, as was Battlefield I, while Assassins Creed was unchanged.
Techspot concludes:
Desktop users have little to worry about in terms of performance loss, particularly gamers. We’ve yet to test older CPUs, but given the type of workloads we’re seeing impacted by the patch, I don’t think there’s going to be an issue with any desktop hardware, but we’ll certainly report back if there is.
The reduction in 4K read performance for high speed NVMe drives is a concern and while this shouldn’t impact any games, any application that is sensitive to this might show a reduction in performance. Of course the brief list of applications I tested showed no real reduction in performance period.
The issue nonetheless remains and is one that has a far bigger potential in affecting servers. It’s a serious concern for data centers both on the side of performance and more importantly, security. That’s not our area of expertise or interest, so we’ll leave that testing to those better equipped to tackle it.
See their full post for all the detail and many more graphs here.
Are any of our readers still planning to avoid the patch? Let us know below.