Microsoft launches Zero Trust Deployment Center
2 min. read
Updated on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
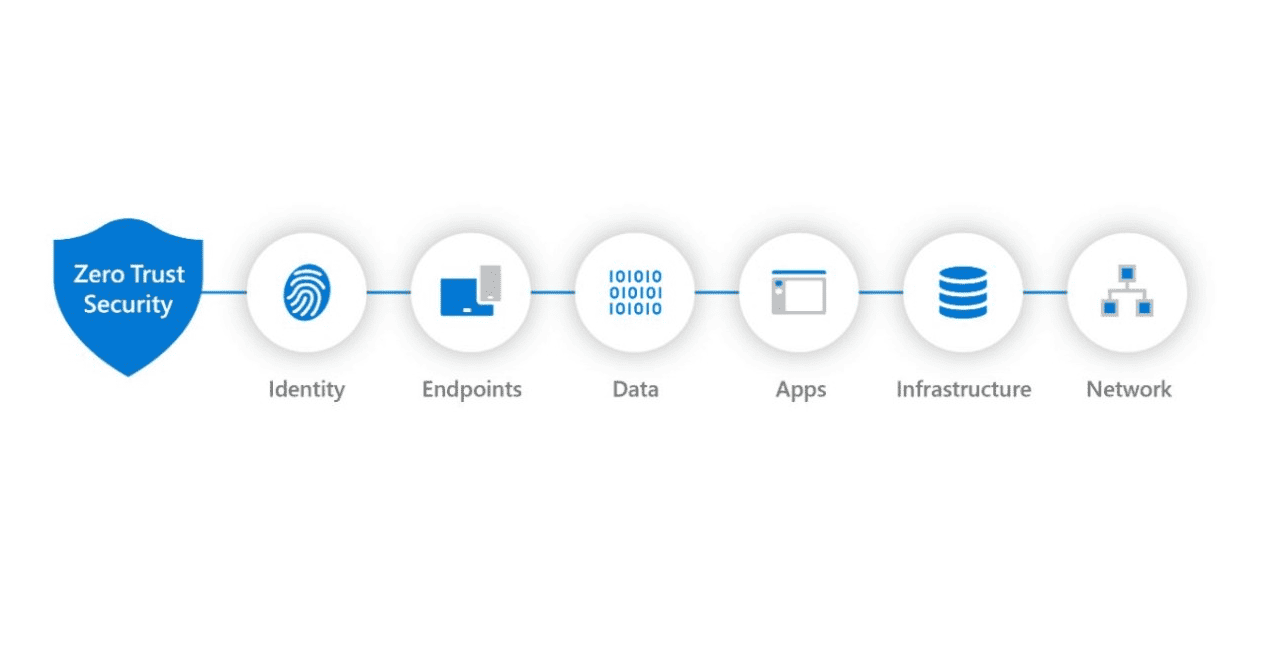
Zero Trust is a networking security management model which assume your internal network is already compromised and works to protect your valuable corporate data despite this.
Microsoft explains the Zero Trust security model as such:
Instead of assuming everything behind the corporate firewall is safe, the Zero Trust model assumes breach and verifies each request as though it originates from an open network. Regardless of where the request originates or what resource it accesses, Zero Trust teaches us to “never trust, always verify.” Every access request is fully authenticated, authorized, and encrypted before granting access. Microsegmentation and least privileged access principles are applied to minimize lateral movement. Rich intelligence and analytics are utilized to detect and respond to anomalies in real time.
The model has come to prominence with the pandemic, due to so many people working remotely, and now Microsoft has launched its Zero Trust Deployment Center to help businesses transitioning to this new way of working.
The deployment centre is a set of guidelines that explains to businesses how to implement principles of Zero Trust, how to up set up infrastructure, network, data, and environment-readiness, with plain-level objectives and action items to ease the environment setup.
The guidance is also useful for as a knowledge repository for organizations that have implemented Zero Trust security models, to benchmark their progress, using Microsoft’s Zero Trust assessment tool here.
Those thinking about implementing the model can check out Microsoft’s guidance here.
via Neowin