Microsoft Defender will now default to automatically "remediating" malware
2 min. read
Updated on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more

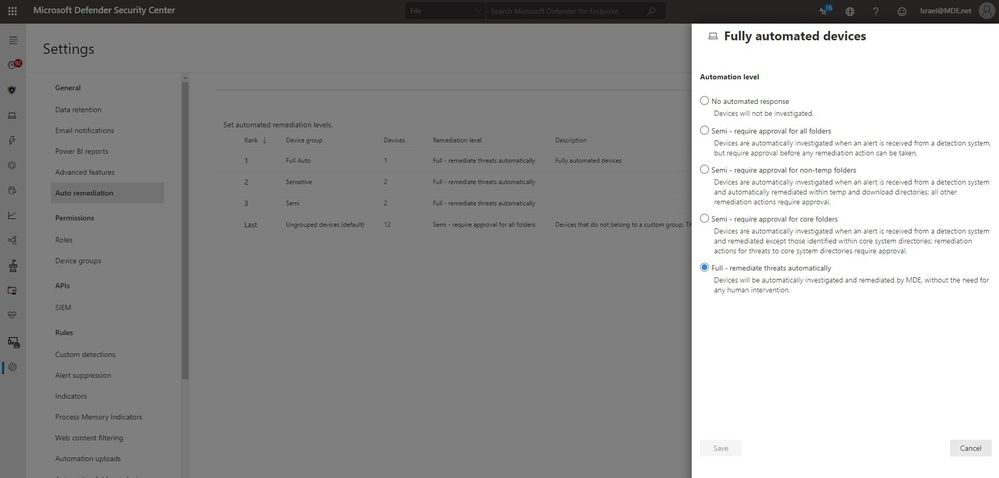
On the Microsoft Security and Compliance blog, Microsoft has just announced that they are switching Microsoft Defender for Endpoint from Require approval for any remediation (semi) to Remediate threats automatically (full), starting with the Public Preview version.
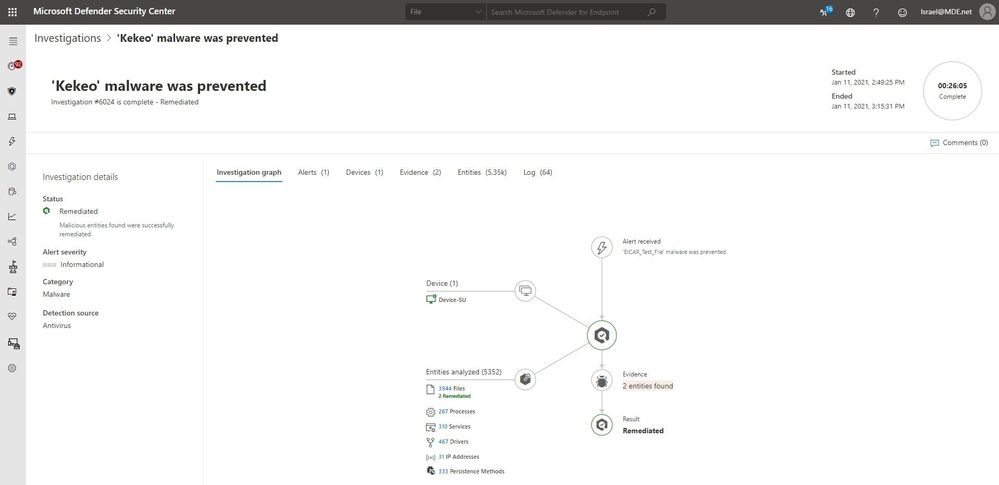
When set to Full – Remediate threats automatically, after a security alert Microsoft Defender will automatically start an investigation, create a list of related entities found on a device and their verdicts (malicious, suspicious, or clean) and for each malicious entity, create a remediation action, and then execute that action to remove or contain a malicious entity.
When set to Semi – Require approval for any remediation, the action will wait for manual approval, with the security team having to connect to the machine.
Microsoft says in practice, when machines are set to remediate threats automatically, 40% more high-confidence malware samples were removed than customers using lower levels of automation. Full automation also frees up customers’ critical security resources so they can focus more on their strategic initiatives. Waiting for approval on the other hand may allow malware to spread to other computers and cause untold harm.
The concern is, of course, an out of control Defender client may cause more harm than good itself, but Microsoft says they have increased their malware detection accuracy, improved their automated investigation infrastructure and importantly added the option to undo remediation actions, meaning clients should always be able to return to a safe state.
Microsoft now recommends automatic remediation and are rolling out the feature by default to the Public Preview version of Microsoft Defender for Endpoint.
Read all about the feature at Microsoft here.