Homeland Security's CISA release Sparrow vulnerability and exploit detection tool for Microsoft 365 networks
2 min. read
Published on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more

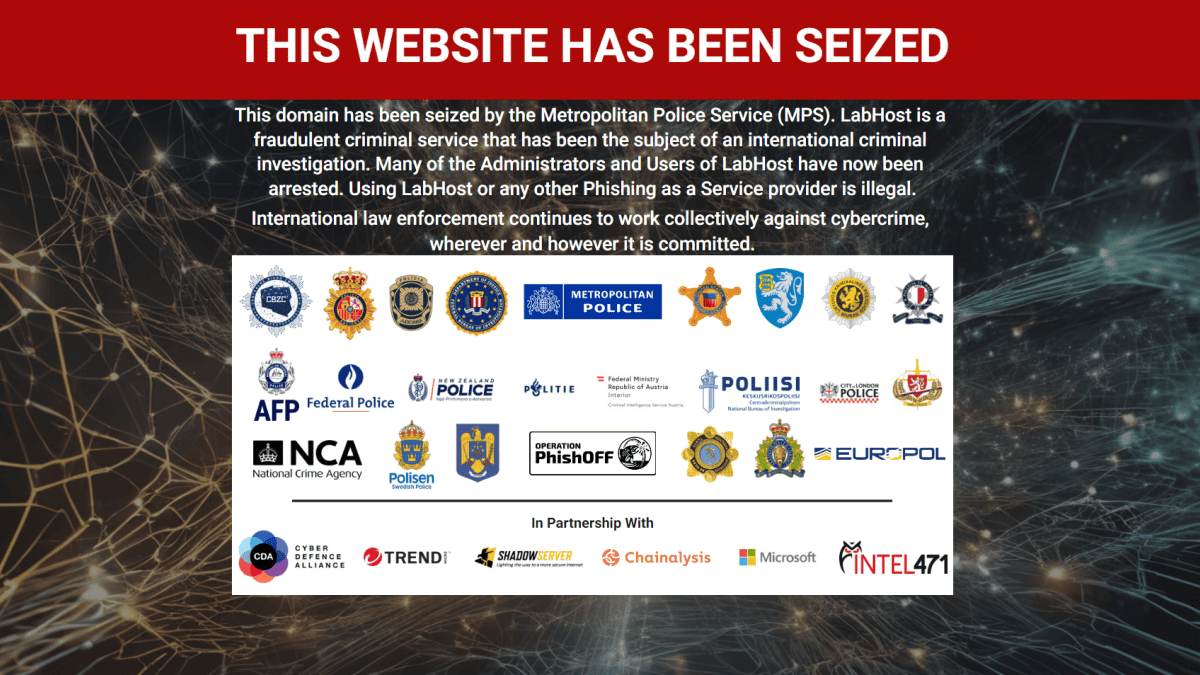
With the recent report that hackers have been exploiting Microsoft 365 to compromise commercial and sensitive government networks, the US Department of Homeland Security’s Cybersecurity & Infrastructure Security Agency (CISA) has released a tool to help network admins secure their Microsoft 365-based infrastructure.
Sparrow.ps1 is a Powershell-based tool created by CISA’s Cloud Forensics team to help detect possible compromised accounts and applications in the Azure/m365 environment. The tool is intended for use by incident responders, and focuses on the narrow scope of user and application activity endemic to identity and authentication based attacks seen recently in multiple sectors.
Sparrow.ps1 will check and install the required PowerShell modules on the analysis machine, check the unified audit log in Azure/M365 for certain indicators of compromise (IoC’s), list Azure AD domains, and check Azure service principals and their Microsoft Graph API permissions to identify potential malicious activity. The tool then outputs the data into multiple CSV files in a default directory.
CISA warns the open-source tool is not a replacement for intrusion detection systems and is neither comprehensive nor exhaustive of available data, and is intended to narrow a larger set of available investigation modules and telemetry to those specific to recent attacks on federated identity sources and applications.
The tool is free to use and can be found at GitHub here.
via theWindowsClub