Dell release fix for remote exploit BIOS flaw affecting 30 million laptops, download yours now
2 min. read
Updated on
Read our disclosure page to find out how can you help MSPoweruser sustain the editorial team Read more
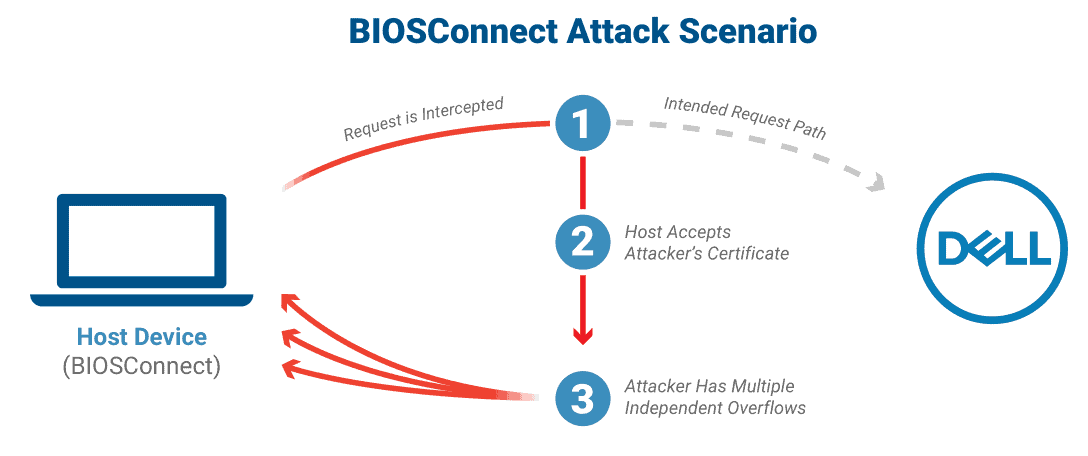
We wrote last week of a flaw in Dell’s remote BIOS update software that opens Dell laptops up to a man in the middle attack which allows attackers to remotely execute code within the BIOS of up to 129 different Dell laptop models.
“Such an attack would enable adversaries to control the device’s boot process and subvert the operating system and higher-layer security controls,” Eclypsium researchers explain.
Eclypsium said up to 30 million devices, which include consumer and business laptops, desktops, and tablets are affected.
At issue is the BIOSConnect feature, which is part of Dell’s SupportAssistant. This feature is pre-installed on most Dell Windows devices.
The service uses an insecure TLS connection from BIOS to Dell and has three overflow vulnerabilities which allow attackers to deliver any software they choose to devices.
Two of the overflow security flaws “affect the OS recovery process, while the other affects the firmware update process,” Eclypsium says. “All three vulnerabilities are independent, and each one could lead to arbitrary code execution in BIOS.”
The researchers say all the devices need to have their BIOS updated, and recommends Dell’s BIOSConnect feature not be used to do this.
Dell has acknowledged the High Impact issue and has today released a fix.
Their support page notes:
DSA-2021-106: Dell Client Platform Security Update for Multiple Vulnerabilities in the BIOSConnect and HTTPS Boot features as part of the Dell Client BIOS
Summary: Dell is releasing remediations for multiple security vulnerabilities affecting the BIOSConnect and HTTPS Boot features.
Visit Dell here and download the patch today.
via thewindowsclub